Smart Contract Security Standards and Principles
Blockchain Development Services | Blockchain for Startups | Blockchain Marketing 101
Over $350 million was lost to crypto exploits in early 2026, with many attacks exploiting weak smart contract security and poorly designed protocols, according to the Reddit.com report on January 2026 crypto hacks. Every second a contract is live, attackers scan for vulnerabilities, and your code is under constant scrutiny.
Modern smart contract development demands structured threat modeling, hardened architecture, rigorous testing, and continuous monitoring.
This guide will show you how to prevent critical smart contract vulnerabilities, implement defensive coding patterns, execute thorough audits, deploy resilient monitoring systems, and prepare a production-ready launch strategy that protects capital and builds long-term trust. Security is not optional. It is infrastructure.
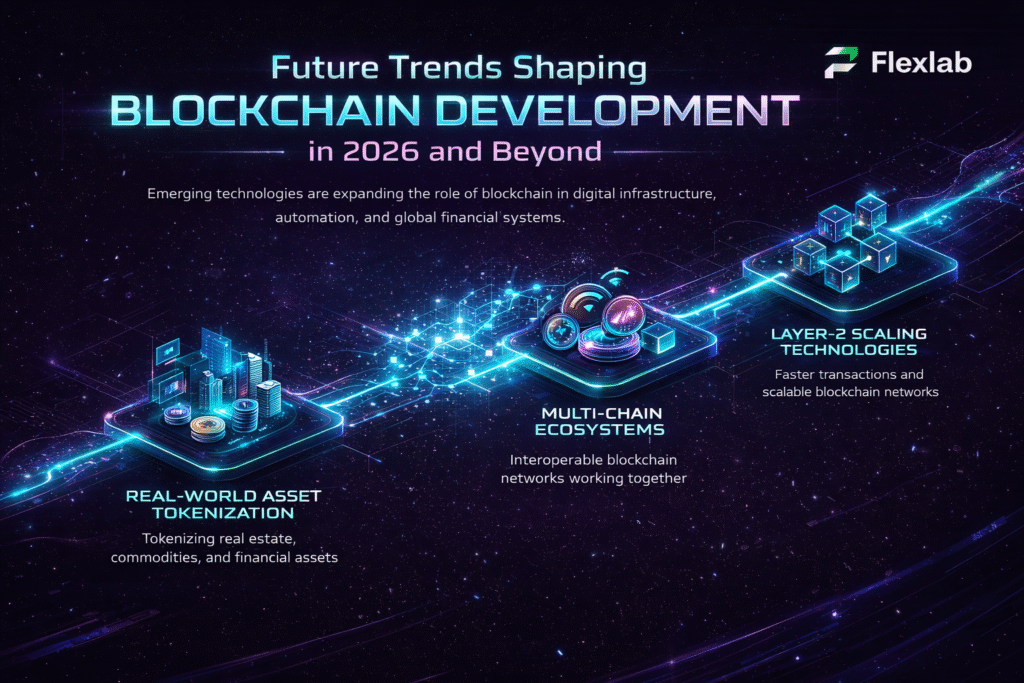
Understanding Smart Contract Security
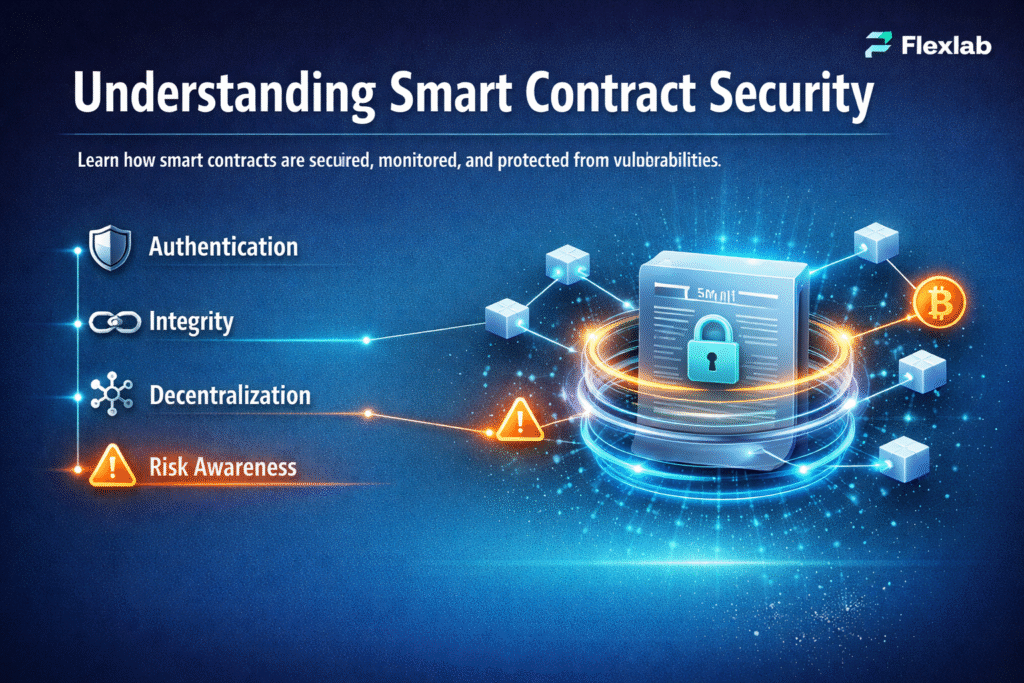
Smart Contract Security is the backbone of any reliable blockchain system within modern blockchain technology ecosystems. Moreover, unlike traditional software, smart contracts are immutable once deployed, meaning any flaw can lead to permanent loss of funds or irreparable damage. Therefore, understanding smart contract security is essential for developers, organizations, and users engaging in decentralized finance or blockchain applications.
As per the CryptoSlate 2026 Report, in 2026 alone, over $350 million in crypto assets were lost due to insecure smart contracts. These incidents highlight why a strong foundation in security practices can prevent catastrophic financial loss. By focusing on smart contract vulnerabilities, threat modeling, and preventive principles, developers can significantly reduce risks before deployment.
What Is Smart Contract Security?
Smart contract security refers to designing, developing, and deploying blockchain contracts written in secure programming languages that are resistant to attacks, function exactly as intended, and preserve the integrity of digital assets. Unlike regular software:
- Contracts are immutable once deployed.
- They handle real financial value in a decentralized, trustless environment.
- They interact with other contracts, oracles, and blockchain protocols.
A secure smart contract ensures code correctness, robust access control, and safe interactions with external systems. By anticipating potential threats, developers protect both funds and user trust in DApps.
Why Smart Contract Security Matters
Every deployed contract carries high stakes. Poor security can result in:
- Financial loss: Millions lost in a single exploit.
- Irreversible consequences: Unlike traditional apps, contracts cannot be patched post-deployment.
- Reputational damage: Users lose trust instantly.
- Regulatory scrutiny: Especially for DeFi or tokenized platforms.
According to CryptoPotato’s 2026 report, over $4 billion was lost globally in crypto hacks, with a majority targeting flawed smart contracts. Therefore, understanding vulnerabilities and planning mitigations is the foundation of blockchain security.
Common Smart Contract Vulnerabilities
Developers must be aware of frequent attack vectors to prevent costly mistakes. Key vulnerabilities include:
| Vulnerability | Description | Potential Impact | Mitigation / Best Practice |
| Reentrancy | External call re-enters contract | Theft of funds, double withdrawals | Checks-Effects-Interactions, reentrancy guards |
| Overflow / Underflow | Math operations exceed limits | Token or balance errors | Solidity ≥0.8 built-in checks, SafeMath |
| Weak Access Control | Unauthorized actors access sensitive functions | Admin abuse, critical failures | Least privilege, multi-sig authorization |
| Oracle Manipulation | Reliance on manipulated external data | Price exploits, fund loss | Multiple oracle feeds, sanity checks |
| Unchecked External Calls | Calls to untrusted contracts without validation | Funds stolen, contract hijacked | Validate inputs, assume callee is hostile |
Understanding these vulnerabilities is the first step toward building secure smart contracts and protecting decentralized ecosystems.
Core Security Principles
Beyond vulnerabilities, several conceptual principles guide secure development:
- Least Privilege: Grant only necessary permissions.
- Defense in Depth: Layered security across code, architecture, and operations.
- Fail-Safe Defaults: Contracts should default to safe states under unexpected behavior.
- Minimize Attack Surface: Only implement essential features.
- Explicit Upgrade Strategy: Plan governance and key management if upgrades are needed.
These principles prepare developers to implement smart contract best practices effectively in later stages of the lifecycle.
Smart Contract Security Best Practices
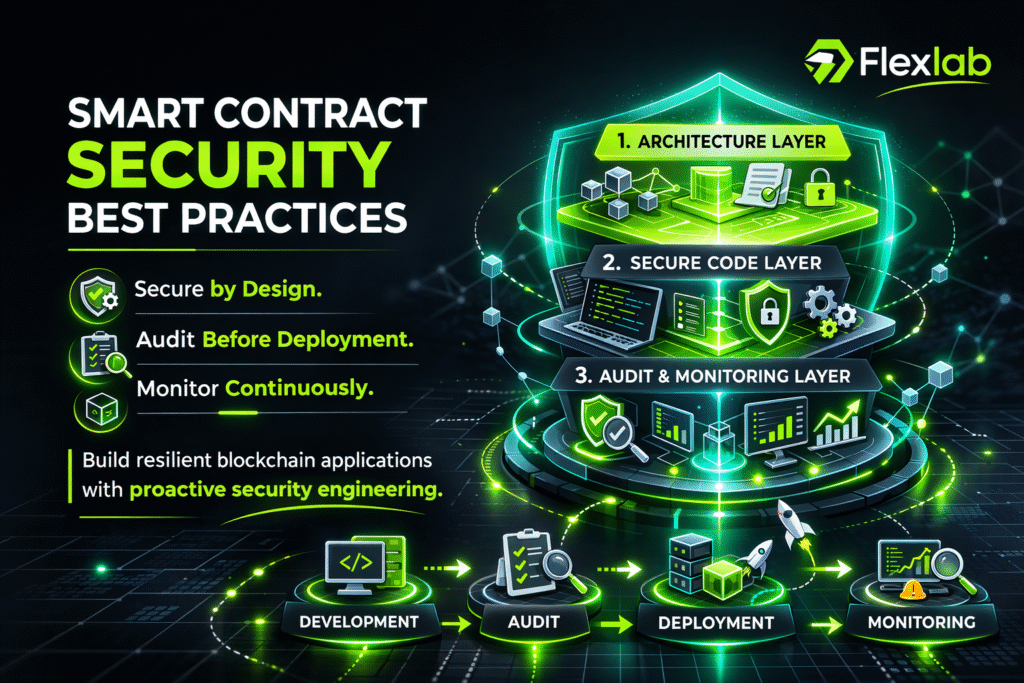
Building secure contracts is about preventing them through disciplined engineering. Additionally, structured review processes, such as a professional smart contract audit, significantly reduce overlooked vulnerabilities.
While understanding vulnerabilities is important, implementing smart contract security best practices is what truly protects decentralized applications from exploitation.
In modern Web3 ecosystems, security must be embedded throughout the design-to-deployment lifecycle. The following practices form the operational foundation of secure smart contract development.
Secure-by-Design Architecture
Security begins before a single line of Solidity is written.
A secure-by-design approach means:
- Clearly defining contract responsibilities
- Keeping logic modular and minimal
- Reducing external dependencies
- Avoiding unnecessary complexity
Over-engineered contracts increase attack surfaces. Instead, developers should separate storage, logic, and access control into clearly structured components.
Threat modeling at the architecture phase helps identify:
- Who could attack the system
- What assets are at risk
- How funds move between contracts
- Which permissions require strict validation
By thinking like an attacker early, teams prevent structural weaknesses later.
Code-Level Defensive Programming
Even well-designed contracts fail without disciplined coding standards. Defensive programming ensures contracts behave safely under unexpected conditions.
Key coding practices include:
- Validate all inputs strictly
- Use require and revert statements properly
- Follow Checks-Effects-Interactions pattern
- Implement reentrancy guards
- Avoid unchecked external calls
- Prefer pull-over-push payment models
Additionally, always use the latest stable Solidity version to benefit from built-in overflow protection and compiler improvements. Secure coding is about writing predictable, auditable code.
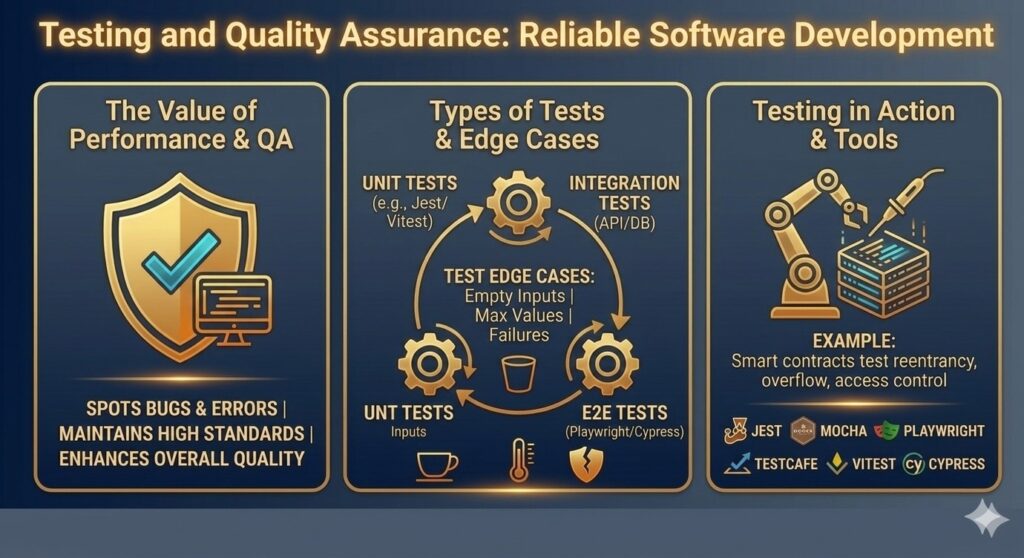
Auditing, Testing, and Continuous Monitoring
Security does not end at deployment. It evolves.
Robust smart contract security includes:
- Automated Testing
- Unit tests
- Integration testing
- Fuzz testing
- Edge-case simulation
- Independent Security Audits
Professional security audits identify logic flaws, gas inefficiencies, and economic attack vectors that internal teams may overlook. - Formal Verification
For high-value protocols, mathematical proofs can verify contract behavior against defined specifications. - Bug Bounty Programs
Incentivizing ethical hackers strengthens community-driven security. - On-Chain Monitoring
Real-time transaction monitoring helps detect suspicious patterns before damage escalates.
Consequently, Security is not a one-time checklist. It is an ongoing discipline.
Benefits of Implementing Best Practices
When development teams combine secure architecture, defensive coding, and continuous validation, they achieve:
- Reduced exploit probability
- Higher user trust
- Improved protocol longevity
- Better compliance readiness
- Stronger investor confidence
In competitive Web3 markets, security maturity differentiates serious projects from risky experiments.
Smart Contract Security Tools and Frameworks
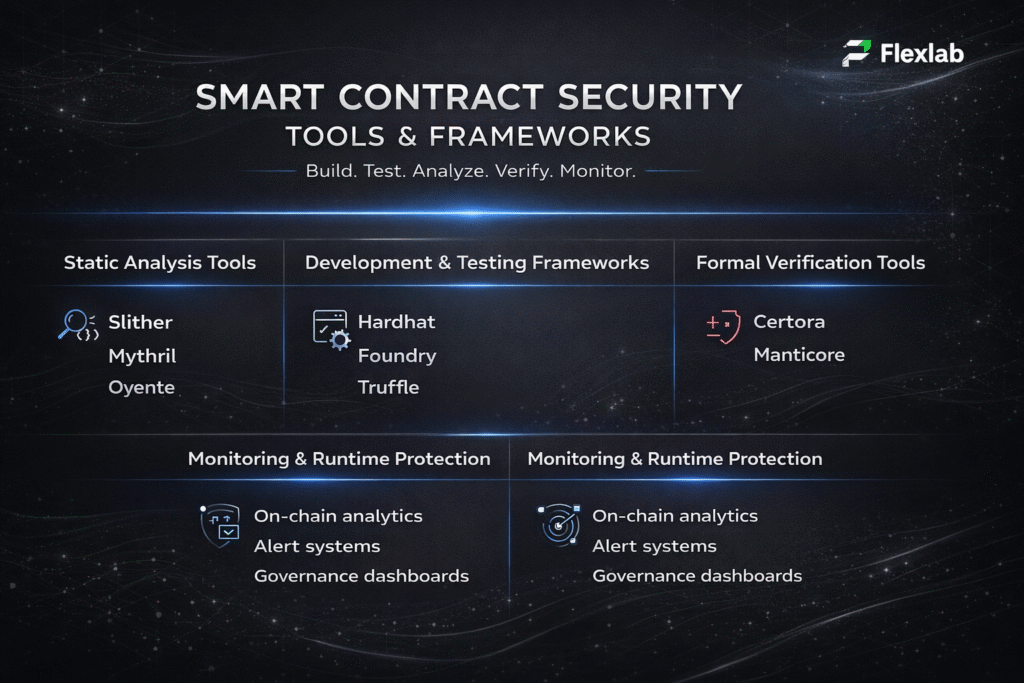
While best practices define what developers should do, tools and frameworks determine how efficiently and accurately they can do it. In modern blockchain ecosystems, relying solely on manual code review is no longer sufficient. Instead, professional teams combine automated analysis, structured testing environments, and advanced verification tools to strengthen smart contract security.
The following categories represent the most widely adopted tools used in secure smart contract development today.
Static Analysis Tools
Static analysis tools examine smart contract code without executing it inside the Ethereum virtual machine. As a result, developers can quickly detect common vulnerabilities, logic flaws, and risky patterns before deployment.
Some of the most widely used tools include:
- Slithe: A Solidity static analyzer that detects reentrancy risks, incorrect inheritance, shadowing issues, and more.
- Mythril: Uses symbolic execution to identify complex security flaws.
- Oyente: One of the early Ethereum contract analysis tools focused on vulnerability detection.
These tools significantly reduce the likelihood of overlooked weaknesses. However, they should complement, not replace, manual review.
Testing and Development Frameworks
Testing frameworks provide structured environments for writing, deploying, and validating smart contracts before mainnet release. Consequently, they improve reliability and smart developer productivity.
Leading frameworks include:
- Hardhat: A powerful development environment with built-in testing, debugging, and plugin support.
- Foundry: A fast, Rust-based toolkit for Solidity testing and fuzzing.
- Truffle: A well-established framework offering testing and deployment pipelines.
By integrating automated unit tests, integration tests, and fuzz testing, teams can detect issues long before contracts handle real assets.
Formal Verification and Advanced Security Tools
For high-value DeFi protocols and enterprise-grade blockchain systems, standard testing may not be sufficient. In such cases, formal verification provides mathematical guarantees about contract behavior.
Advanced tools and approaches include:
- Certora: Allows developers to define security rules and mathematically verify contract compliance.
- Manticore: Performs dynamic symbolic analysis for detecting deeper logic issues.
Although formal verification requires additional expertise, it dramatically increases assurance levels for critical systems.
Monitoring and Runtime Protection Tools
Security does not end at deployment. Therefore, runtime monitoring tools play a crucial role in detecting anomalies, suspicious transactions, or exploit attempts in real time.
Modern approaches include:
- On-chain analytics platforms
- Transaction monitoring systems
- Automated alert mechanisms
- Multi-signature governance dashboards
By continuously observing contract behavior, projects can respond quickly to abnormal patterns and minimize potential damage.
Key Advantages of Security Tools
Combining static analysis, structured testing, formal verification, and runtime monitoring creates a multi-layered defense strategy. Each tool addresses a specific risk individually. Together, however, they form a comprehensive smart contract security framework capable of protecting high-value blockchain applications.
Ultimately, secure development is not just about writing safe code. It is about building an ecosystem of tools that continuously validate, monitor, and strengthen contract integrity.
Comparison of Leading Smart Contract Security Tools and Frameworks
To help developers and blockchain teams, especially every smart contract developer responsible for production systems, choose the right solution, the following comparison highlights the strengths, ideal use cases, and limitations of the most widely adopted smart contract security tools and development frameworks. Each tool plays a different role within a comprehensive smart contract security strategy.
| Tool | Category | Primary Purpose | Best For | Strength | Limitation |
| Slither | Static Analysis | Automated vulnerability detection | Early-stage code review | Fast execution and developer-friendly reports | Limited deep economic analysis |
| Mythril | Symbolic Execution | Advanced security flaw detection | Complex exploit discovery | Detects multi-transaction attack paths | Slower than lightweight analyzers |
| Hardhat | Development Framework | Testing and deployment environment | Structured development workflows | Rich plugin ecosystem and debugging tools | Requires configuration setup |
| Foundry | Testing Toolkit | Solidity testing and fuzzing | High-performance test environments | Extremely fast and powerful fuzzing | Steeper learning curve for beginners |
| Certora | Formal Verification | Mathematical contract validation | Enterprise-grade DeFi protocols | Provides formal security guarantees | Higher complexity and resource requirements |
Choosing the Right Security Tool for Your Needs
Although no single tool guarantees complete protection, combining static analysis, structured testing frameworks, and formal verification tools creates a layered smart contract security framework. As a result, development teams can significantly reduce exploit risks while improving reliability and investor confidence.
Emerging Risks and Challenges in Smart Contract Security

While smart contract security practices continue to improve, new risks are evolving just as quickly. As blockchain adoption expands across DeFi, enterprise ecosystems, and cross-chain infrastructures, the overall attack surface continues to widen.
For this reason, understanding modern security challenges is essential for long-term resilience and sustainable growth.
Rising Technical and Economic Complexity
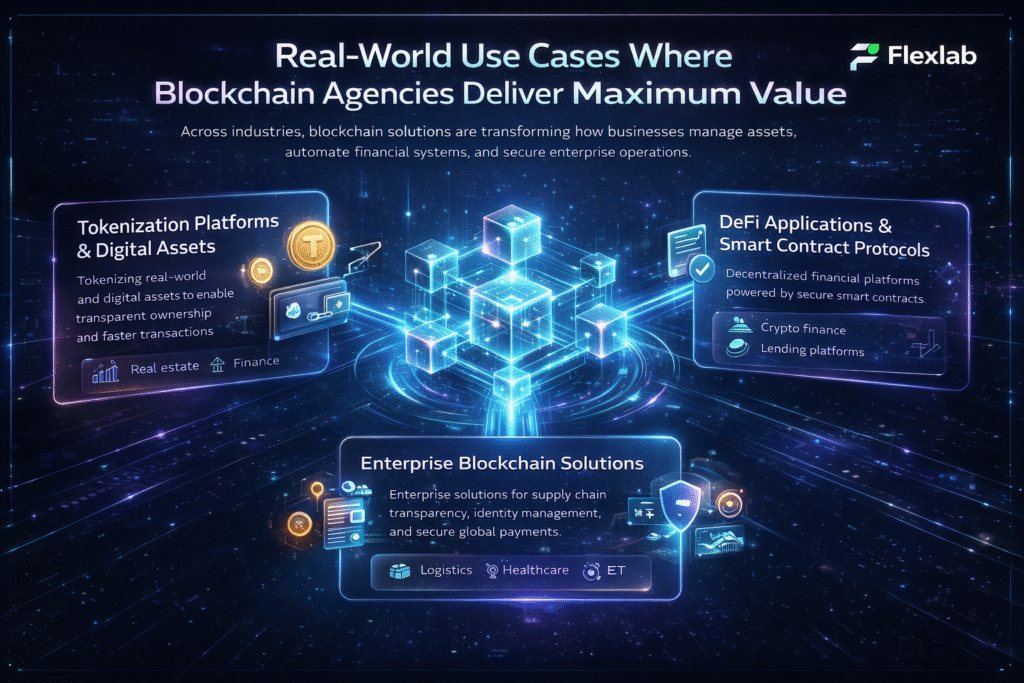
As decentralized finance protocols become more advanced, their underlying smart contracts grow significantly more complex. In particular, multi-layer integrations, automated liquidity strategies, oracle dependencies, and composability between protocols increase the likelihood of hidden vulnerabilities.
At the same time, economic attack vectors such as flash loan exploits and market manipulation introduce risks that traditional code audits may not fully capture. Instead of targeting syntax errors, these attacks exploit weaknesses in financial logic and game theory. Consequently, developers must evaluate not only technical security but also economic design risks when building secure smart contracts.
Cross-Chain and Governance Weak Points
With the rapid expansion of cross-chain bridges and multi-network deployments, new systemic vulnerabilities have emerged. Because bridges often custody large volumes of locked assets, they naturally become high-value targets for attackers.
Moreover, governance mechanisms and access control systems introduce additional exposure. For example, poorly designed admin privileges, upgrade functions, or DAO voting structures can enable malicious actors to manipulate contracts or seize control. As a result, secure key management, strict role-based permissions, and governance audits are becoming indispensable components of modern smart contract security frameworks.
Regulatory and Operational Uncertainty
Beyond technical vulnerabilities, regulatory scrutiny is increasing across global markets. As governments introduce evolving compliance requirements around digital assets and DeFi, projects must adapt quickly to avoid legal and financial consequences.
Additionally, operational risks such as weak key storage practices, misconfigured deployments, or insufficient monitoring tools can undermine even well-audited contracts. In many cases, security failures occur not during development but during deployment or maintenance. In particular, a weak configuration of deployment tools can expose contracts to avoidable operational risks.
Therefore, smart contract security must extend beyond code reviews. Ultimately, it requires operational discipline, compliance awareness, and continuous risk management to remain effective.
The Future of Smart Contract Security
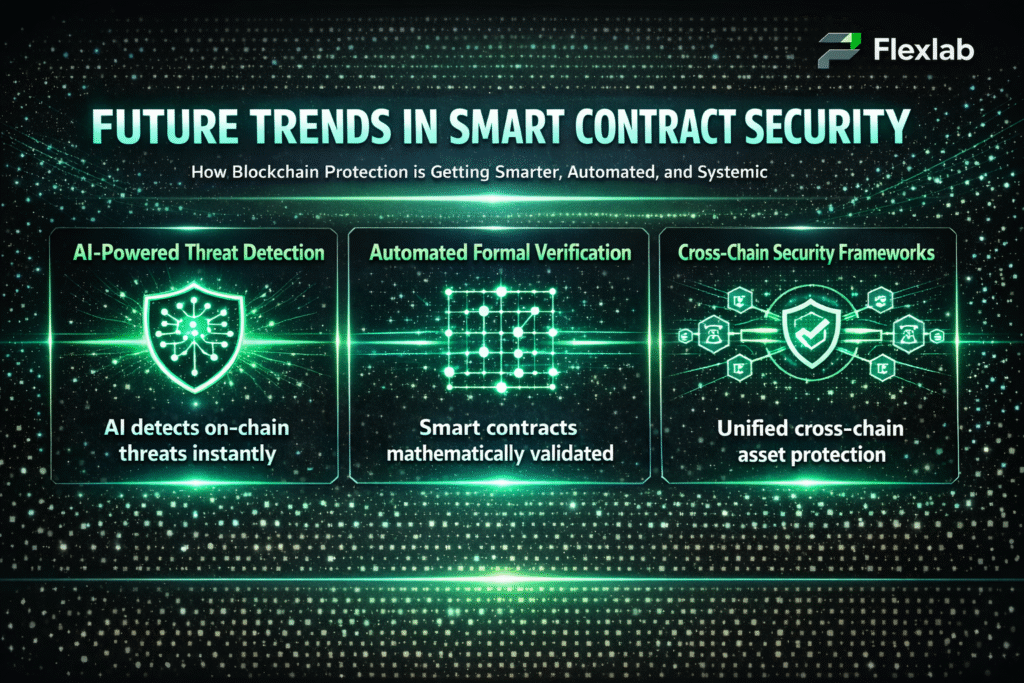
As blockchain ecosystems continue to mature, smart contract security is evolving from reactive patching to proactive, intelligent protection. Projects are now integrating automated monitoring, AI-powered vulnerability detection, and systemic defenses to prevent attacks before they occur.
For developers and organizations, anticipating future threats is essential to maintain trust, resilience, and regulatory compliance.
-
AI-Powered Vulnerability Detection
Artificial intelligence is transforming how smart contracts are secured. Unlike traditional audits, AI-driven systems can analyze behavioral patterns and implement real-time anomaly detection, thereby identifying previously unseen attack vectors.
As a result, this enables real-time detection of unusual contract interactions, governance manipulations, and potential exploits; consequently, it reduces human error and, in turn, accelerates response times.
-
Automated Formal Verification
Automated formal verification is making high-assurance smart contracts accessible to more projects. By integrating verification into development pipelines, teams can mathematically validate contract logic before deployment.
As a result, this ensures that contracts behave exactly as intended; consequently, it significantly lowers the risk of bugs, economic exploits, and unintended interactions across blockchain networks. Moreover, by reinforcing predictable behavior, it strengthens overall system reliability and trust.
-
Ecosystem-Level and Cross-Chain Security
As decentralized applications increasingly operate across multiple chains, security must extend beyond individual contracts.
Future strategies will focus on:
- Securing cross-chain bridges and interoperability layers
- Implementing unified monitoring dashboards
- Reducing single points of failure in governance and access control
As a result, this shifts security from contract-level defense to system-wide resilience; consequently, it protects value across entire blockchain ecosystems, thereby strengthening overall network stability and trust.
Why This Matters
Smart contract security is no longer optional; it is a competitive advantage. Projects that integrate AI, automation, and systemic protections will not only withstand attacks but also attract more users, investors, and regulatory trust.
Ultimately, the future of smart contract security depends on intelligent design, proactive monitoring, and cross-chain resilience.
Real-World Smart Contract Security Examples

While smart contract security frameworks continue to improve, real-world examples show that vulnerabilities can still cause significant financial and reputational damage. By examining these cases, smart contract developers and organizations can better understand how theoretical risks translate into practical consequences.
More importantly, these examples highlight the importance of proactive design, rigorous testing, and continuous monitoring.
The DAO Exploit (Reentrancy Vulnerability)
One of the earliest and most influential smart contract failures occurred with The DAO, where a reentrancy vulnerability allowed an attacker to withdraw funds before balances were updated repeatedly.
As a result, millions of dollars worth of ETH were drained, ultimately leading to a historic hard fork of the Ethereum network. This case demonstrated how a single overlooked logic flaw can reshape an entire ecosystem.
-
Security Insight from The DAO Exploit
Always protect against reentrancy attacks using checks-effects-interactions patterns and secure coding standards.
Cross-Chain Bridge Exploits
As cross-chain bridges gained popularity, they became high-value targets for attackers. Several bridge vulnerabilities allowed malicious actors to mint or withdraw assets without proper validation.
Because bridges often hold large liquidity pools, these weaknesses resulted in substantial losses across multiple ecosystems. These events exposed the risks of centralized validators, flawed signature verification, and weak monitoring systems.
-
Bridge Security Takeaway
Therefore, secure cross-chain validation mechanisms and implement multi-layer verification.
Flash Loan and Economic Manipulation Attacks
Flash loans introduced a new category of economic exploits. Instead of attacking code directly, attackers manipulated market prices and protocol logic within a single transaction.
Consequently, DeFi protocols with weak oracle protections or flawed pricing formulas suffered significant losses. These attacks proved that economic design vulnerabilities can be just as dangerous as coding errors.
-
Oracle & Pricing Defense Strategy
Combine technical audits, economic stress testing, and Oracle security reviews.
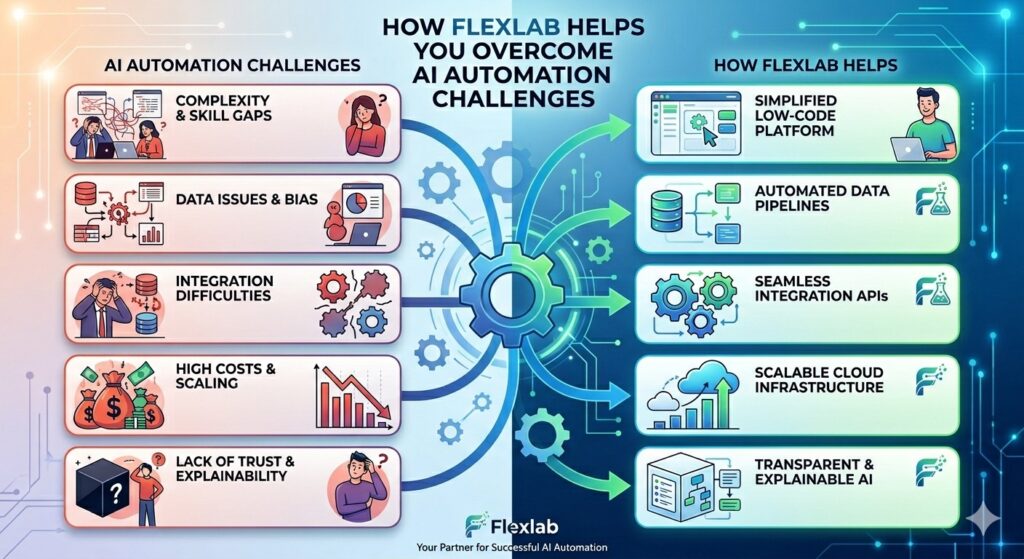
Why Leading Teams Trust Flexlab for Smart Contract Security?

Every exploit begins as an overlooked assumption. Every loss begins as an unchecked vulnerability. In modern blockchain ecosystems, delay is exposure. Precision is protection. Flexlab engineers hardened smart contract architectures designed to withstand evolving attack surfaces, economic manipulation, and cross-chain complexity.
Ready to Strengthen Your Smart Contract Security Strategy?
📞 Book a FREE Consultation Call: +1 (416) 477-9616
📧 Email Us: info@flexlab.io
Explore our services to see how secure architectures are engineered from the ground up. Review our portfolio to examine real-world blockchain security implementations across decentralized and AI-driven ecosystems.
If your protocol handles real values, now is the time to evaluate its resilience. Connect with us through our contact us page and initiate a focused security discussion.
For ongoing insights on blockchain protection, advanced verification, and AI-powered security intelligence, visit our website, explore the latest perspectives on our blog, or follow us on LinkedIn to stay ahead of emerging exploit patterns and industry shifts.
Read more:
- How to Become a Blockchain Developer?
- The Role of Blockchain Audit in DeFi, NFTs, and Web3 Security
- How Public Key Vs Private Key Works in Blockchain Security?
Final Words on Smart Contract Security
Smart contract security determines whether blockchain innovation survives real-world pressure. Code executes exactly as written. Flaws execute just as precisely.
Taken together, best practices, testing frameworks, real-world failures, and emerging threats all point to one clear standard: discipline at every layer.
First, architecture must be intentionally designed for resilience. Next, verification must rigorously validate assumptions and logic. Furthermore, continuous monitoring is crucial for detecting anomalies early. Finally, economic design must align incentives to prevent exploitation.
In short, discipline is not optional; rather, it is required at every stage and across every layer.
Security is not a feature release. It is structural integrity. Protocols built on rigorous smart contract security endure. Those who ignore it disappear. In decentralized systems, security is the only lasting foundation.
Can smart contracts be protected from zero-day exploits?
Not completely. Audits and testing reduce known risks, but unknown vulnerabilities can still exist in complex logic or third-party integrations. That’s why continuous monitoring matters. In addition, bug bounties and upgrade mechanisms create a safety net. Security isn’t about being flawless; it’s about being prepared.
Do security audits really increase user trust?
Absolutely. When users deposit funds into a protocol, they are trusting code, not people. Therefore, public audits and transparent security reports signal professionalism and accountability. On the other hand, one major exploit can permanently damage credibility. Strong security practices build confidence before users even connect their wallets.
Are upgradeable contracts safer than immutable ones?
It depends on the structure. Upgradeable contracts allow fixes if vulnerabilities are discovered, which reduces long-term risk. However, they introduce governance and access control concerns. Immutable contracts remove upgrade risk, but mistakes cannot be corrected. The safest approach balances flexibility with strict permissions and clear governance rules.