Can Day Trading Become a $1,000-a-Day Income?
Crypto Trading Bot | Common Mistakes in Crypto Transactions | Hot Wallet vs Cold Wallet
Can you make $1000 a day by day trading? Yes, you can, but it’s extremely challenging and requires significant capital, deep knowledge, strict discipline, and a robust strategy. However, without a proper plan, most of the traders lose money, especially those with small accounts.
Small accounts like $1,000 can get you started for learning, but they carry huge risks. Hitting $1,000 daily profits requires much larger capital, enough for smart position sizes, loss buffers, and steady percentage gains over chasing big daily targets.
Want to learn more? Let’s dive into the helpful insights and get aware of when to start day trading!
What is Day Trading?
Day trading is the process of buying or selling financial assets on the same trading day. The purpose is to generate short-term profit in price movements rather than long-term growth. In contrast to long-term investors or swing trading approaches, day traders close all their positions before the market closes to reduce overnight and exchange rate risk in global markets.
Moreover, it depends on intraday market volatility triggered by news, earnings, or economic data. It also analyzes real-time charts, volume, and momentum indicators through specialized day trading platforms or algorithmic trading tools. In the US, FINRA classifies a pattern day trader. They executed four or more day trades in five business days, as it requires at least $25,000 in a margin account. Meanwhile, active day traders can invest 12% of daily stock volume despite only 25% of Americans trading stocks post-2021 surge.
According to Investopedia, the main idea is to capitalize on daily market volatility, whether prices rise or fall. Traders rely on intraday price action and repeatable setups during the session, often using electronic communication networks (ECNs) for faster execution.
How Does Day Trading Work?
Day trading basically focuses on short-term price fluctuations that are primarily driven by immediate market responses to breaking news, earnings reports, Federal Reserve announcements, and other macroeconomic data, sparking volatility in stocks, forex, futures, and even options trading.
Traders dive into intraday charts, such as 1-minute, 5-minute, or 15-minute timeframes. They use candlestick patterns, trendlines, spread trading opportunities, and order flow to define high-probability entry and exit points. Volume spikes signal institutional participation, while volatility metrics like Average True Range (ATR) help gauge risk-adjusted position sizing for optimal opportunity capture.
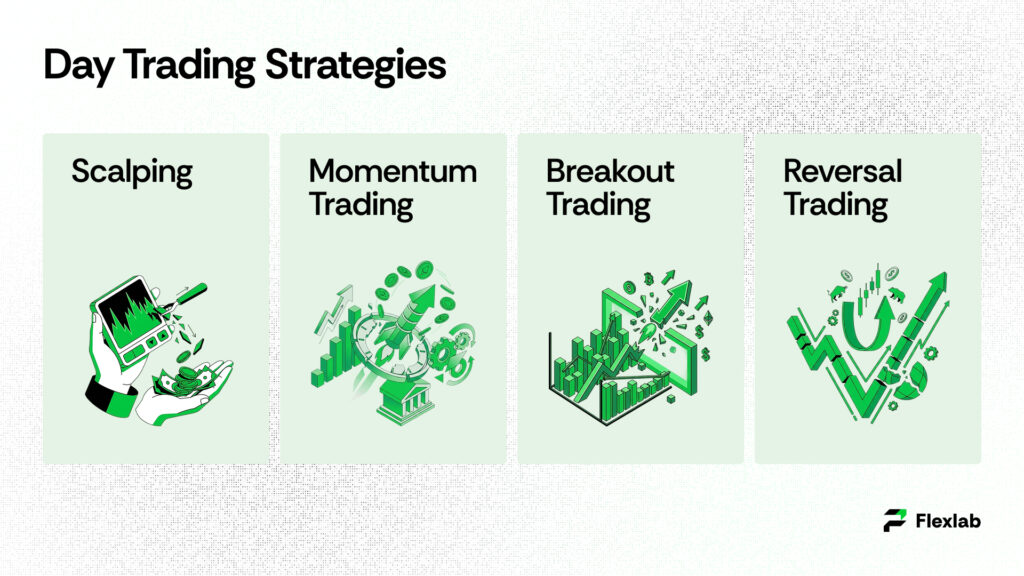
Let’s read some of the most popular day trading strategies:
-
Scalping
Scalpers execute numerous small trades throughout the session. It targets 5-10 cent gains per share of that compound via 50-100+ setups daily. Scalpers hold positions that last from seconds to a few minutes, thriving on low-latency platforms, tight spreads, and Level 2 quotes to gain a high-frequency trading order flow advantage. Scalping strategies rely heavily on ultra-fast day trading software and ECN routing, and their success depends on commission rebates and avoiding too many trades in ranging markets.
-
Momentum Trading
Momentum trading strategies chase strong price trends sparked by positive catalysts, such as merger rumors, analyst upgrades, earnings beats that exceed estimates, or sudden trading spikes. They buy when prices are increasing (“buy high, sell higher”) and add to positions on dips while using VWAP as a guide. Moreover, it also uses trailing stops with parabolic SAR until signs such as chart divergences or volume peaks signal that the trend is fading.
-
Breakout Trading
Breakout traders look for prices stuck in narrow ranges or flag patterns near important horizontal lines (such as past highs/lows or pivot points). They confirm a breakout with rising volume (at least 1.5 times the average) and a strong close above/below that level, then jump in aggressively. Targets are set using measured moves (e.g., add the range’s height to the breakout point), with stops placed just below the key level for protection. Many algorithmic trading systems automate these breakout rules for consistency.
-
Reversal Trading
This reversal strategy detects signs of exhaustion when prices reach extreme levels, such as overbought or oversold conditions, accompanied by declining volume or chart discrepancies. Traders sometimes apply contrarian investing principles, entering against the trend using candlestick patterns like pin bars, rejecting key Fibonacci retracement levels, and checking multiple timeframes for agreement. Trades aim for 1:2 or better risk-reward ratios, with trailing stops to manage the high odds of failure when betting against momentum.
The most common technical indicators that refine these setups include Moving Averages, Bollinger Bands, the Relative Strength Index (RSI), and Volume Analysis.
Day Trading Tips for Beginners
Here are the practical tips for day trading for beginners to stay safe and strategically:
- Start with a Demo Account
- Develop a Clear Trading Plan
- Focus on Liquid Assets
- Master Risk Management
- Use Simple Technical Analysis
- Control Emotions and Stay Informed
Start with a Demo Account
First, you need to use paper trading or a demo account. Explore platforms like TradingView or broker demos to learn and evaluate how orders, charts, and execution work without having any real risk. This is also the ideal time for back-testing your day trading strategies and learning how to day trade with data instead of emotions.
Develop a Clear Trading Plan
Make a proper plan that defines entry and exit rules, profit targets, and max daily loss (e.g., 1-2% of capital per trade) before any position.
Focus on Liquid Assets
Trade high‑volume liquid stocks like AAPL, MSFT, or NVDA. These offer smooth entries/exits and low slippage, which is critical for active trading, spread trading, and strategies sensitive to execution quality.
Master Risk Management
Set stop-loss orders, avoid overleveraging, and never revenge trade after losses. Understand cash vs margin account differences before using leverage, and size positions using volatility measures such as ATR to align risk with market volatility.
Use Simple Technical Analysis
Start with candlesticks, support/resistance, moving averages, and VWAP; avoid indicator overload.
Control Emotions and Stay Informed
Don’t get caught up in market hype. Stick to the data and technical analysis guidelines. Moreover, review trades daily to refine strategies and do informal back testing to understand the pros and cons of day trading for your personality. Additionally, monitor news, earnings, and economic data impacting markets to stay informed.
Stay Informed
Monitor news, earnings, and economic data impacting markets.
How to Start Day Trading?

Are you wondering how to day trade? Look no further! We’ve compiled detailed steps below. Professional day traders possess deep market expertise, established routines, and the skill to generate consistent income. Moreover, it often works as a full-time business rather than just a gambling.
Follow these structured steps to launch effectively:
- Learn and get aware of a good deal about the market and how to leverage fundamental and technical analysis.
- Make sure you have enough capital to comply with day trading rules, and never put more on the line than you can afford to lose.
- Develop and follow personalized trading criteria, such as entry/exit rules or risk parameters, and stick with them.
Let’s dig into each step for detailed insights for better clarity.
1. Gain Extensive Market Knowledge and Experience
Traders who don’t possess prior basic knowledge of market fundamentals end up losing money. You must hold a working knowledge of technical analysis and chart reading for a good start. New traders blindly jump in and lose big because charts alone trick them without understanding what drives price swings, including sector shifts or global news events.
Furthermore, learn the basics on platforms like TradingView, where you can read candlestick patterns, spot support/ resistance levels, and access tools like RSI and MACD. Additionally, you have to focus on specific assets like tech stocks, for example, jump or drop fast on Fed interest rate news. Do practice safely by paper trading on simulators for 3-6 months and test trading strategies on past data. Moreover, learn about PDT rules, like under the amount of $25k, you’re limited to three day trades in five days, or you get flagged. Note that 80% of big moves come from just 20% of volatile stocks during market hours.
2. Ensure You Have Adequate Capital
A professional day trader only risks capital that they can afford to lose. It is 1% capital per trade to survive drawdowns. Day trading profits are tiny (just pennies per share), so start with $30k or more to trade bigger sizes; margin accounts give 4 times your cash buying power, but a 25-30% drop triggers forced sales.
Quick stat: 2025 FINRA data shows 72% of underfunded day traders who break rules get restricted, while well-funded ones handle 10-20 trades daily without emotions messing them up.
3. Master Trading Discipline
Many day traders lose their money because they didn’t follow any criteria. Success is impossible without following a discipline. It is said that “plan your trade and trade your plan” can cut losses by 50%. Day traders rely on market volatility for profit. A day trader finds a stock attractive if it jumps around a lot, often triggered by events like earnings reports (better or worse than expected), shifts in investor mood, or broader news about the economy or company. Therefore, these ups and downs create chances to buy low and sell high quickly.
Common Risks in Day Trading
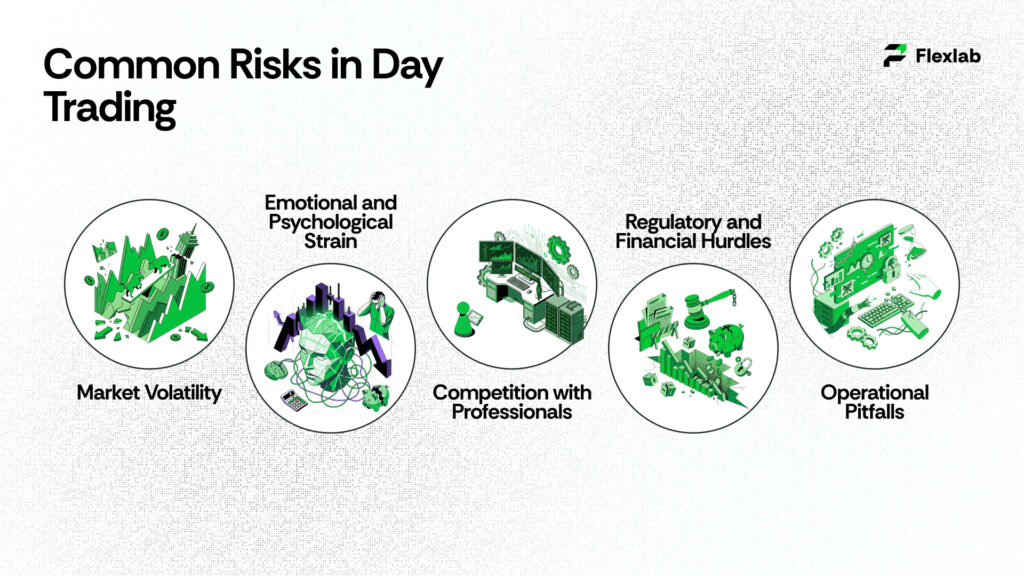
Day trading exposes participants to amplified risks beyond typical investing due to high leverage, speed, and emotional pressures.
Market Volatility
Stock prices shuffle up rapidly within minutes. Losses can accumulate faster without proper stop-loss orders. Moreover, leveraged bets make it worse.
Emotional and Psychological Strain
Fear and greed of traders lead them into overtrading or revenge trades. As a result, they lose money through transaction fees and quit trading within a year.
Competition with Professionals
Retail faces HFT bots and institutions with faster tech and data edges, making consistent wins rare.
Regulatory and Financial Hurdles
PDT rule demands $25k minimum, while commissions and slippage erode slim profits—average day trader nets -4.5% annually post-fees.
Operational Pitfalls
Technical glitches, latency, or low liquidity trap exits, and taxes treat gains as ordinary income (up to 37%).
Day Trading Example
A day trade works like any regular stock trade, but you buy and sell the stock all within the same trading day, sometimes just seconds or minutes apart.
For example, imagine a trader analyzes Intuitive Sciences Inc. (ISI), a Nasdaq 100 stock. Their technical analysis reveals a clear pattern: whenever the Nasdaq rises more than 0.4%, ISI climbs at least 0.6% on most days. The trader sees signs that this will happen today.
At market open, the trader buys 1,000 shares of ISI. They wait for it to hit that 0.6% gain target, then sell the entire position right away for quick profit.
This is classic day trading. Hence, it ignores ISI’s long-term investment value and purely exploits the short-term trend. If ISI drops 0.8% against the pattern instead? The trader sells immediately anyway and accepts the loss.
Is Day Trading Legal In The US?
Day trading remains fully legal in the US, governed by rigorous, global-leading regulations that safeguard investors and promote market integrity. The SEC, FINRA, and CFTC lead oversight of intraday activities, enforcing transparency, fraud prevention, and fair practices. The SEC via EDGAR filings and enforcement, FINRA rules on broker conduct/SIPC protection, and CFTC on futures/forex.
Central is the PDT Rule: executing four or more day trades in five business days in a margin account designates you a Pattern Day Trader, mandating $25,000 minimum equity; dips trigger 90-day restrictions or cash-only limits.
Margin trading follows Fed’s Regulation T (50% initial margin), but brokers impose house rules like 25% maintenance for PDTs, curbing leverage risks amid volatility; non-compliance risks, calls, or liquidations.
Is $1000 Good to Start Trading?
$1,000 is enough to start trading in the US, but it is not sufficient for frequent day trading due to the $25,000 Pattern Day Trader (PDT) rule on margin accounts. Beginners can instead use it for swing trading, options, futures, or cash accounts with low- or no-minimum brokers like Interactive Brokers or Moomoo.
-
PDT Limitations
Executing four or more day trades in five business days flags a margin account as PDT, requiring $25k equity; falling below restricts to cash buys or settles trades T+1/T+2, halting intraday flips. With $1000, limit to three weekly day trades or avoid margins entirely.
-
Feasible Alternatives
Opt for futures (e.g., Micro E-mini on NinjaTrader, $50 margins) or forex where PDT skips, risking 1% ($10) per trade for 1-3% daily targets ($10-30 gains). Brokers like OANDA or Plexytrade enable $0-50 starts with demos for practice.
-
Realistic Expectations
About 72% of day traders lose money each year. A $1,000 account requires ultra-tight risk (0.5–1% stops), limiting gains to about $10–$20 per day before fees erode any edge. Growth should come from compounding, not leverage.
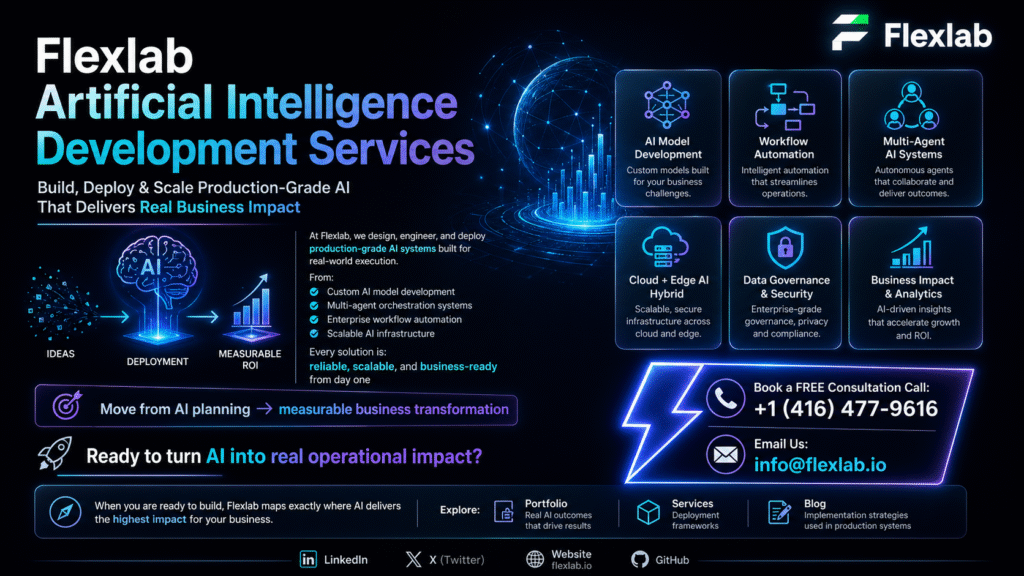
Unlock Profitable Day Trading with Flexlab’s AI Power – Start FREE!

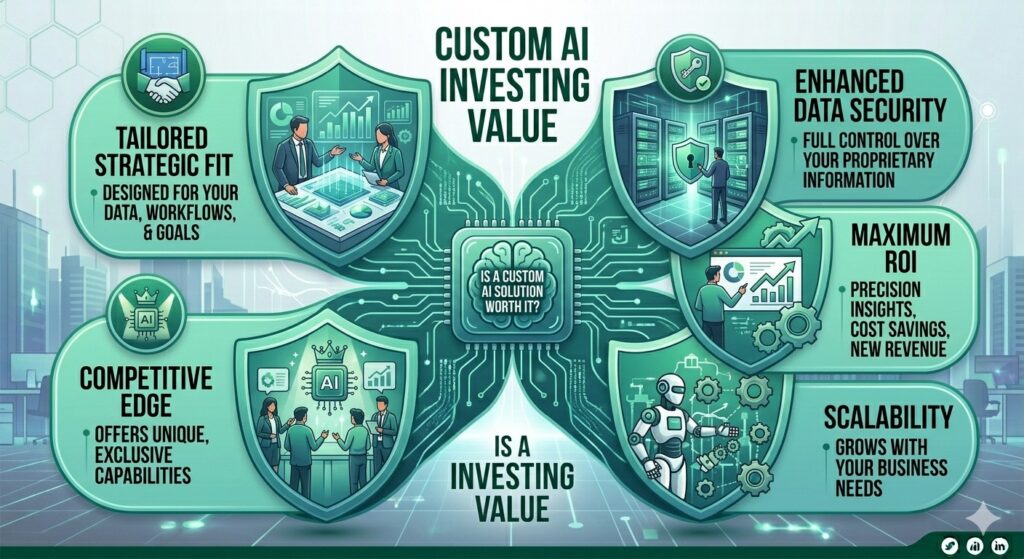
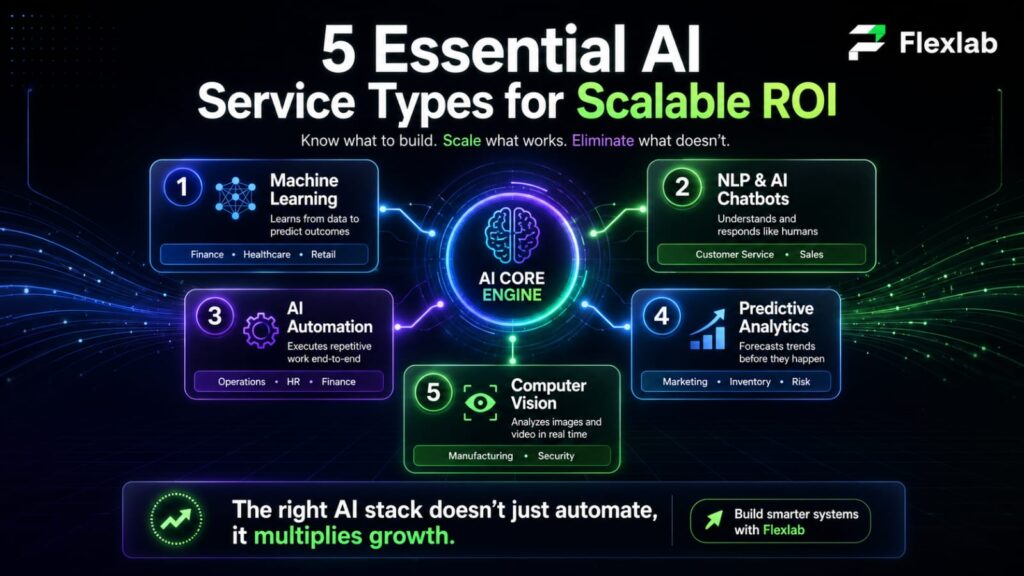
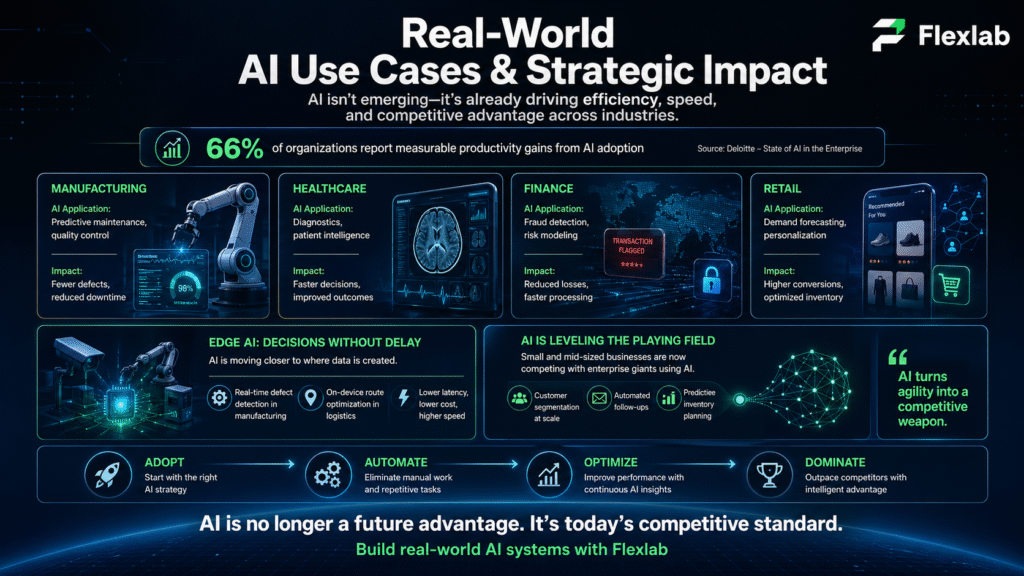
Tired of 90% trader failure rates, PDT restrictions, and manual charting chaos? Flexlab’s elite blockchain/AI developers build your custom trading bot in 30 days – or it’s FREE until perfect. Automate breakouts, scalping with Level 2 + VWAP, real-time volatility alerts (ATR>2%), and 1:2 R: R risk management that slashes emotional losses.
Save 80% vs hiring in-house. Moreover, instant access to pre-vetted experts for backtesting trading, multi-timeframe scanners, and broker APIs (TradingView/Interactive Brokers). Scale from $1k demos to live $25k+ accounts without coding.
Claim Your FREE Technical Audit + 30-Min Strategy Session Today! Contact us now and visit our LinkedIn page.
Ready to Master Day Trading Without the Losses?
📞 Book a FREE Consultation Call: +1 (416) 477-9616
📧 Email us: info@flexlab.io
Conclusion
Day trading offers high-reward potential through volatility but demands $25k+ capital, iron discipline, and proven edges—90% fail without them. Start with Flexlab demos, master the tips above, and treat it as a skill-built business, not gambling, for sustainable profits over FOMO trades. Discover more about the Blockchain and AI blog: Smart Contract Development, How to Invest in Cryptocurrency, Role of Blockchain Audit in DeFi, NFTs, and Web3 Security, Public and Private Keys, and Benefits of Using a White Label Crypto Exchange.
FAQs
Q1: How is day trading different from swing trading?
Day trading buys and sells stocks within one day, closing all positions before market close to avoid overnight risk. Swing trading holds positions for days or weeks to capture larger price swings. Day trading demands constant screen time and fast decisions; swing trading allows part-time monitoring. Day traders chase tiny intraday moves, while swingers target multi-day trends.
Q2: How much does the average day trader make?
Most day traders lose money, studies show 90-97% net negative annually after fees. Skilled pros average 0.5-2% daily returns on capital, but “average” retail traders lose 4-10% yearly. With $25k, consistent winners might net $10k-50k/year; beginners often bust accounts fast. Success hinges on rare edge + discipline, not typical income.
Q3: Why do you need $25,000 to be a day trader?
FINRA’s Pattern Day Trader (PDT) rule requires $25k minimum equity in margin accounts for unlimited day trades. Executing 4+ day trades in 5 business days flags you as PDT; below $25k limits you to 3 trades/5 days or restrictions. It protects undercapitalized traders from leverage wipeouts via forced sales. Cash accounts or futures/forex bypass PDT but limit scale/speed.